Introduction
In today’s fast changing cybersecurity world, stakeholders need a clear view of the organization’s security. Our team has created an Endpoint Security and Network Solutions Canvas using Elastic Stack to quickly understand security risks in the endpoints. This canvas brings together endpoint alerts and network activity, so one can quickly see what is happening across the company’s systems.
Elastic Defend integration has been used to monitor and protect endpoints from threats. It helps detect suspicious activities, possible attacks, and unusual patterns in real time.
This simple and clear view can help executives understand important risks, make better decisions, and focus on the most critical security issues. It can also help the organization respond faster to threats and keep business operations safe.
Endpoint Threat Monitoring Dashboard
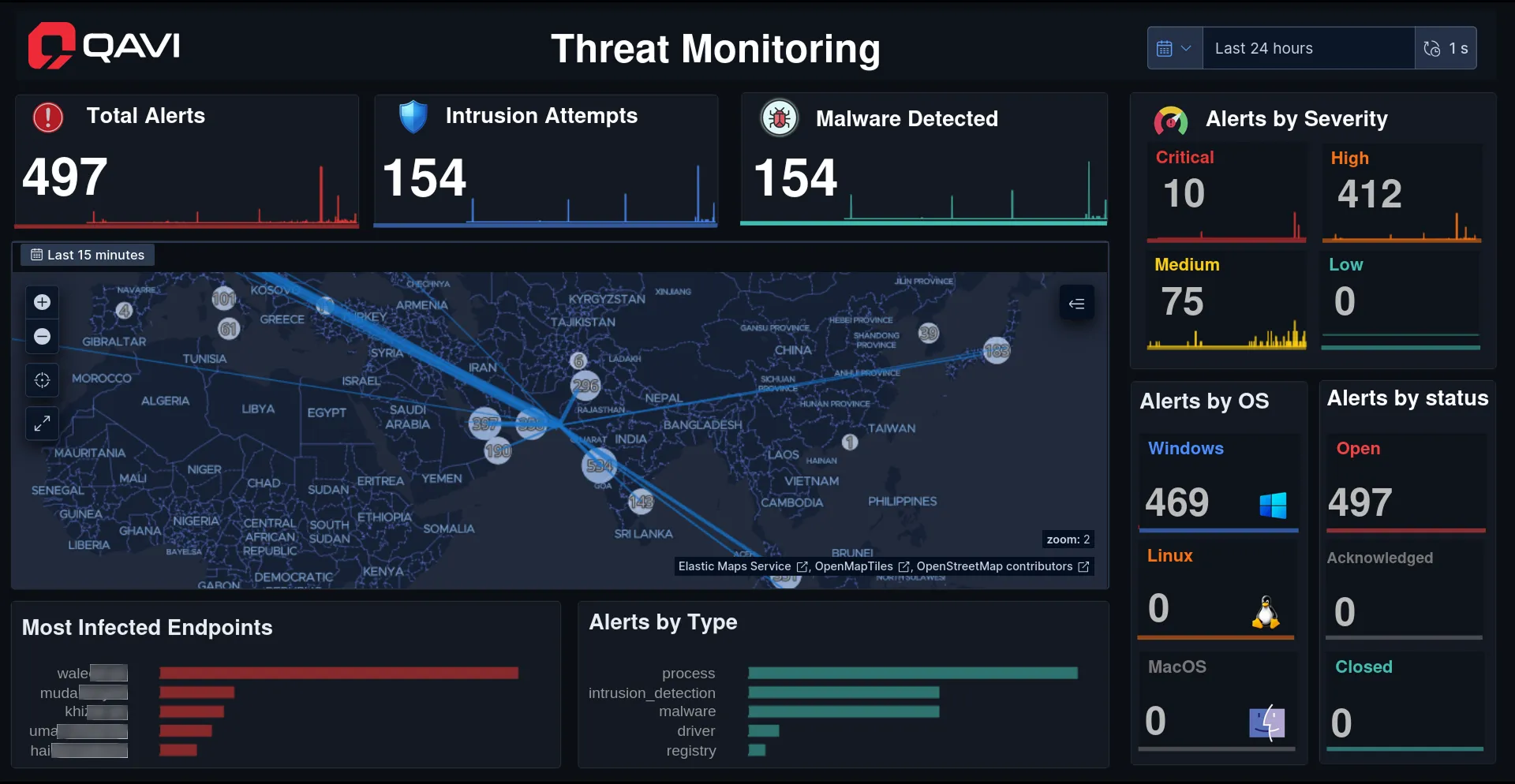
Threat monitoring canvas tracks important metrics to quickly show security risks which are as follows:
- Total alerts represent unusual activity and violations. High alert numbers often point to active attacks or system problems.
- Intrusion and malware insights give early warnings by showing unauthorized access attempts. Acting on these metrics quickly helps stop attacks from spreading.
- Severity based prioritization sorts alerts into critical, high, medium, and low levels. This helps focus on the most urgent risks first and ensures serious issues are not missed.
- Breaking down alerts by OS reveals platform specific weak points. This metric exposes where patches or protections are lacking, Security rules can also be adjusted to fit the environment better.
- Alert status tracking shows which alerts are open, acknowledged, or closed. This helps make sure all risks are handled properly and identifies delays or bottlenecks in the investigation process.
- Infected endpoints show devices with the most alerts. These devices may be compromised and need immediate isolation and scanning to prevent threats from spreading.
- Understanding alert types shows the methods attackers use, like changing processes or modifying system files. This helps improve defenses and refine monitoring rules for better protection over time.
Network Security Monitoring Dashboard
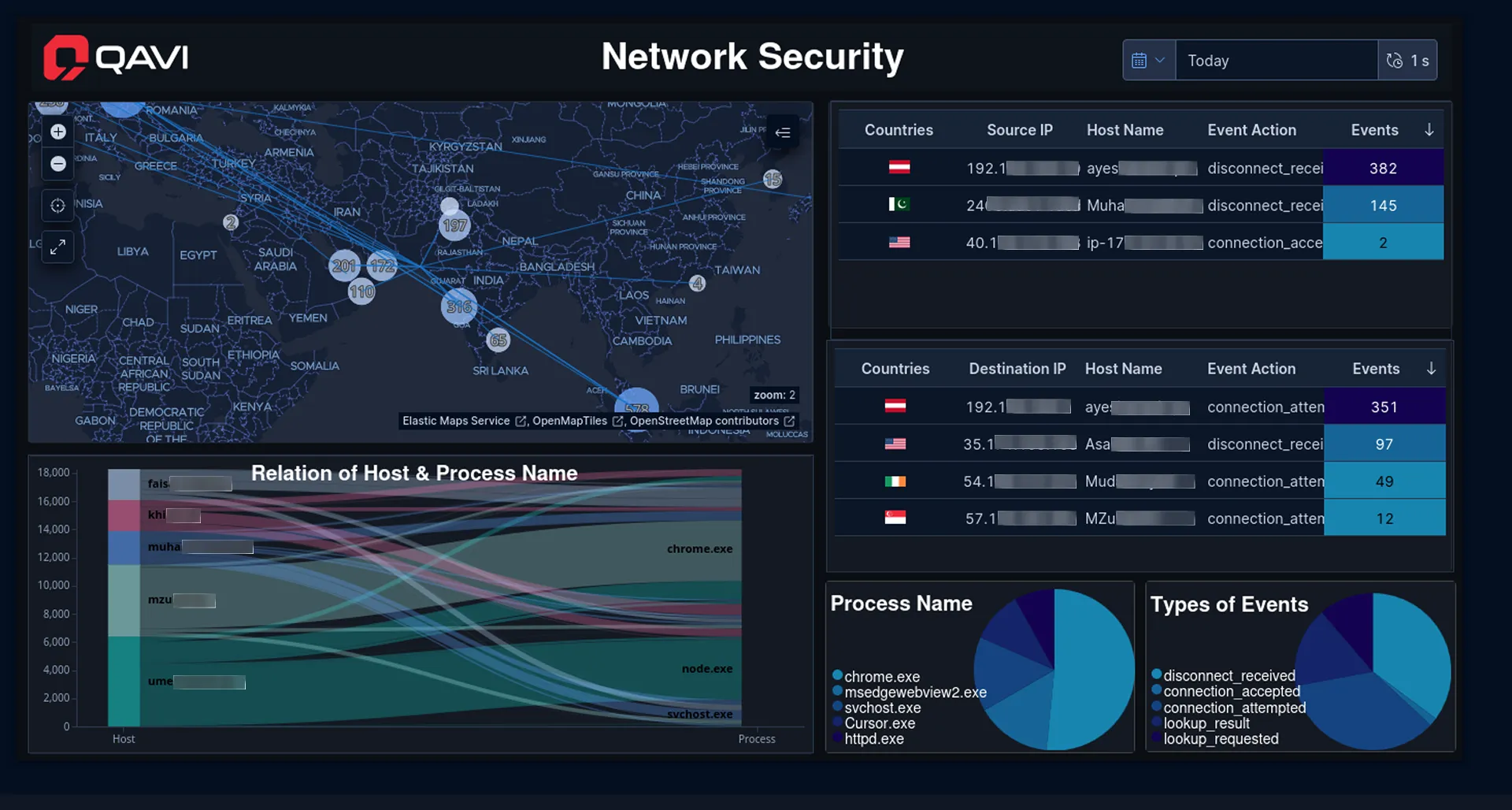
Network security canvas built with Elastic Stack helps monitor network activity to find unusual behavior.
- Source analysis makes it easier to identify the most active sources and detect unusual behavior, enabling quick blocking or closer monitoring of potentially risky sources.
- Destination analysis reveals where connections are being made. This helps identify unauthorized connections and potential security risks.
- Process distribution shows which applications are running most often. This highlights unusual programs or potential malware.
- Event action charts group activities such as connections and disconnections. These charts show normal network behavior, and deviations can indicate problems like what events are occurring over for suspicious activity.
- Sankey charts map connections between hosts and processes and display data flows. Unusual relationships can reveal possible compromises.
If you want to know more on how to add country flags in Kibana. You can check out this blog
Conclusion
As cyber threats get more advanced and harder to predict, relying on separate monitoring tools is not enough. Canvas powered by Elastic where threat alerts and network data give a complete view of an organization’s security. They transform information from endpoint alerts, intrusion attempts, malware activity, process behavior, and network interactions into clear, actionable insights. This enables faster problem detection, smarter responses, and more effective management of security issues.
Unusual activity can be quickly interpreted to potential endpoint risks, reducing blind spots and helping focus on the most important alerts. This approach allows problems to be prevented before they grow, resources to be used more efficiently, and the organization to move from reacting to threats to stopping them early.
Ultimately, comprehensive Canvas like these are more than visualization tools, they are foundational to building resilience in modern cybersecurity.

